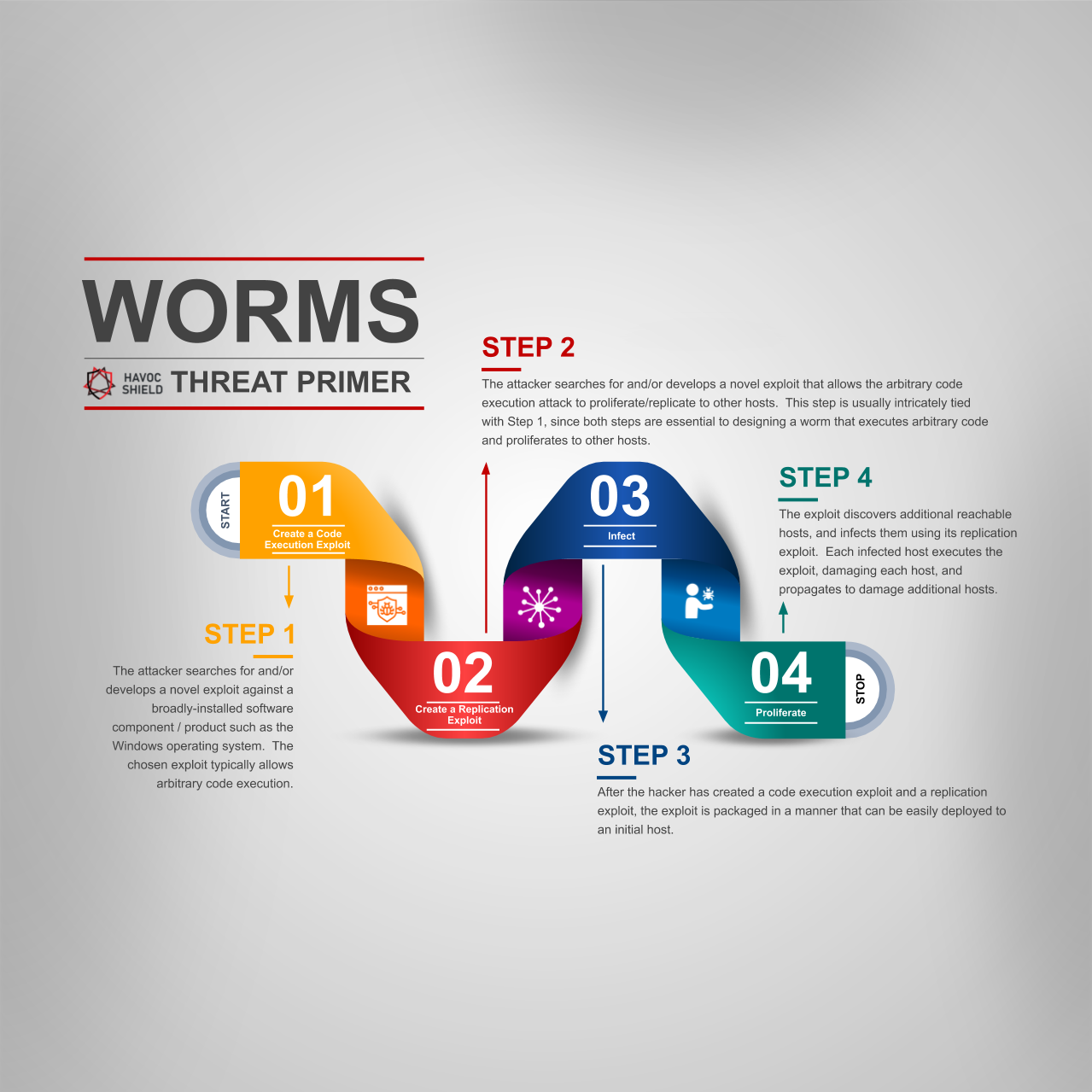
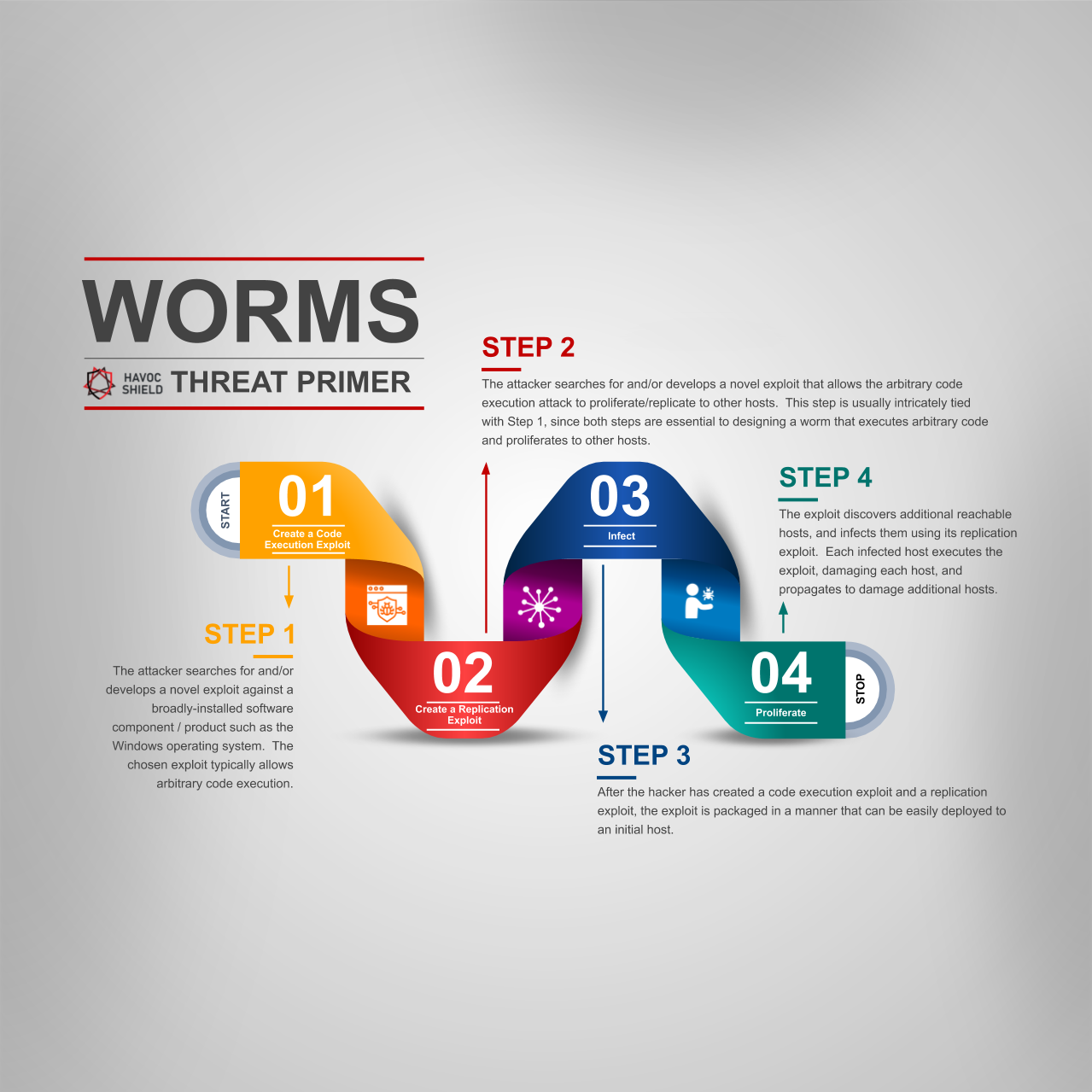
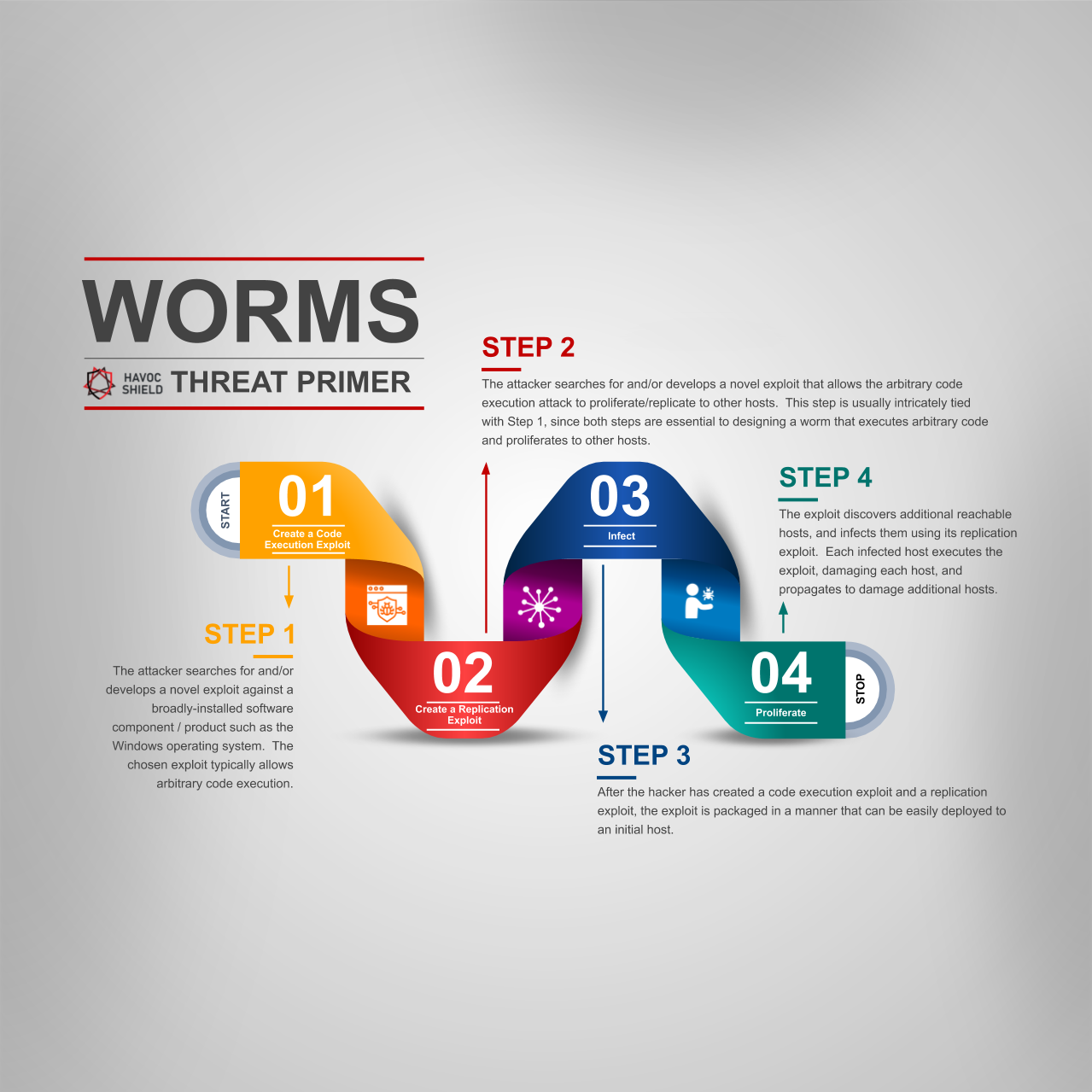
A worm is a self-propagating code execution attack that causes damage on each host that it infects. In less technical terms, a worm is a virus that causes damage, then finds another host to propagate to. This process repeats until it is stopped in its tracks by some effective mitigation, or until it cannot find any additional hosts to transfer to. Here are the key steps that attackers use to implement this type of attack.
Create a Code Execution Exploit
The attacker searches for and/or develops a novel exploit against a broadly-installed software component / product such as the Windows operating system. The chosen exploit typically allows arbitrary code execution.
Create a Replication Exploit
The attacker searches for and/or develops a novel exploit that allows the arbitrary code execution attack to proliferate/replicate to other hosts. This step is usually intricately tied with Step 1, since both steps are essential to designing a worm that executes arbitrary code and proliferates to other hosts.
Infect
After the hacker has created a code execution exploit and a replication exploit, the exploit is packaged in a manner that can be easily deployed to an initial host.
Proliferate
The exploit discovers additional reachable hosts, and infects them using its replication exploit. Each infected host executes the exploit, damaging each host, and propagates to damage additional hosts.
Well-Known Attacks
Some well-known "wormable" attacks include:
- The Morris Worm (1988): many consider this to be the first widespread worm that used the internet in its replication exploit. The exploit relied on the Unix sendmail program and the fingerd service.
- Michelangelo (1991): this worm, activated on Michelangelo's birthday (March 6), proliferated amongst MS-DOS hosts and rewrote the master boot record.
- SMBGhost (2020): this worm spreads amongst Windows 10 hosts. The Department of Homeland Security issued an notice urging the patching of all Windows 10 hosts.
Many other worms have occurred throughout the years, but these three each have unique historic elements. Need help thinking through a strategy to defend against this type of attack? We're here to help.
Interested in more articles in our Threat Primer series? Continue here:
Any additional suggestions for article topics for our Threat Primer series? Drop us a note in the comments section below!