Tech Startup Primer on FedRAMP Security Controls Baseline
December 17, 2020
Cyber Security
Welcome to our post for tech startups seeking to sell cloud-based services to the federal government. As a warm welcome before getting deep into the FedRAMP Security Controls Baseline, here are a few words from fedramp.gov about the nature of the overall program:
"FedRAMP provides a standardized approach to security assessment, authorization, and continuous monitoring for cloud products and services used by the US government. Because its goal is to protect US citizen data in the cloud, it is government’s most rigorous security compliance framework."
If you love endless security questions whose meaning is hard to decipher and even harder to demonstrate that you've complied with, you'll love FedRAMP.
FedRAMP Security Controls Baseline - One Example "Control"
There's no use hiding it. If you are headed towards FedRAMP compliance, and you are a tech startup, you've got some work ahead of you -- and the work centers around certain "controls" that you are expected to implement (and document). A plain language example of a control (stated more simply than what you'll see in FedRAMP) is that you'll be required to have minimum password complexity constraints in your system. The FedRAMP language around that particular control requirement is known as IA-5 (1), and reads as follows:
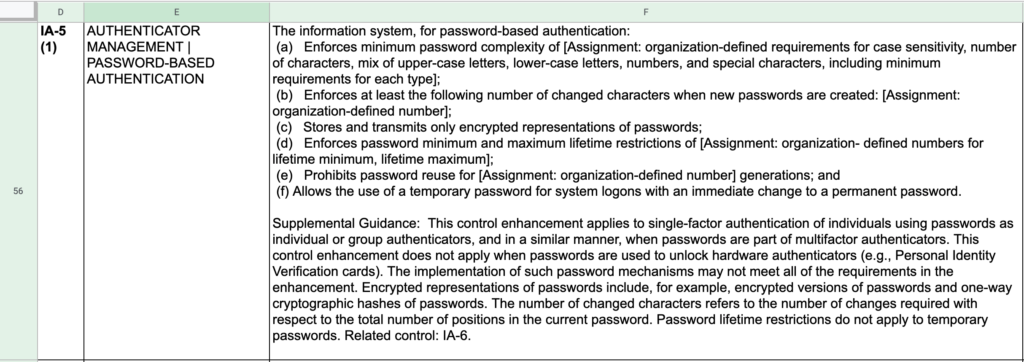
Here's a spoiler for you: assuming your company's offering relies on a third party authentication library or mechanism, it's going to become important that you vet that vendor (and any replacements) for their ability to comply to this control. If you have dependencies that don't comply with FedRAMP, and you have no way to modify the innards of that dependency, you'll quickly get stuck in the FedRAMP controls satisfaction process with no easy path forward.
FedRAMP Control Families
Now that we've talked through an example control -- both a plain language example and it's more elaborate FedRAMP cousin, lets talk about the breadth of controls that you'll be expected to implement as part of FedRAMP. FedRAMP controls are categorized/grouped by "family" -- here are the 17 families of controls that exist in the FedRAMP Security Controls Baseline:
- ACCESS CONTROL
- AUDIT AND ACCOUNTABILITY
- AWARENESS AND TRAINING
- CONFIGURATION MANAGEMENT
- CONTINGENCY PLANNING
- IDENTIFICATION AND AUTHENTICATION
- INCIDENT RESPONSE
- MAINTENANCE
- MEDIA PROTECTION
- PERSONNEL SECURITY
- PHYSICAL AND ENVIRONMENTAL PROTECTION
- PLANNING
- RISK ASSESSMENT
- SECURITY ASSESSMENT AND AUTHORIZATION
- SYSTEM AND COMMUNICATIONS PROTECTION
- SYSTEM AND INFORMATION INTEGRITY
- SYSTEM AND SERVICES ACQUISITION
There are three different breadths of controls lists that you might potentially need to comply with; they are known as "low baseline", "moderate baseline", and "high baseline" -- and it'll take a separate post to go into depth on how you'll get a sense for which of those buckets is the correct one for your company's offering. However, suffice it to say that if there is a way for you to be positioned for the "low baseline" bucket, that would be very helpful. In play here is the question of how many distinct controls you will be asked to implement, document, and comply with:
- Low Baseline: 125 controls
- Moderate Baseline: 325 controls
- High Baseline: 421 controls
One might hope (although, incorrectly) that the low baseline might omit some entire control families. Unfortunately, that's not the case. Here are the control counts, by family, for each of the three baseline levels:
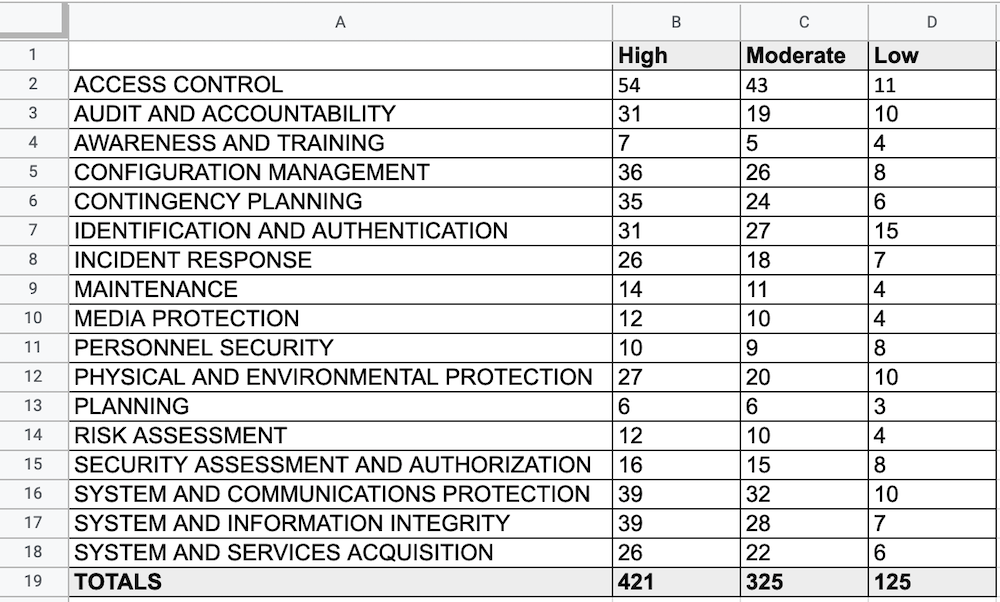
Although each baseline level has multiple controls required in each family, you'll notice that some -- e.g. Access Control -- tail off dramatically from the 54 controls required in the High Baseline to merely 11 in the Low Baseline. However, other controls families have less gradiation -- the Awareness and Security family only shrinks from 7 to 4 as you look across the different baseline levels.
Working Towards FedRAMP Security Controls Baseline Success
We've got a confession to make; we've been holding out on you: here is the direct link to the FedRAMP Security Controls Baseline spreadsheet with the full list of controls for all families and baseline levels. As you review it, remember that what you are fundamentally doing is thinking about how to fulfill controls. And how to implement the controls for each family in a coordinated effort since you'll experience crossover between the activities you do to fulfill one control in a family, with activities you'll want to do to fulfill another control in the same family. Lastly, let's all just hope that your solution ends up being one that works out for the Low Baseline level (125 controls instead of the 421 controls required for High Baseline) -- but that's a topic that we'll have to save for a later post.